Introduction
A port is a 16-bit number used in TCP/IP (Transmission Control Protocol/Internet Protocol) networking in combination with the IP Address of a computing device to for applications and services to communicate between devices.
In this post I will go over details of how and how a port is created and used.
What is a Port in TCP/IP Networking?
A port is a virtual endpoint for communication between devices. Similar to how an IP address is used to identify each computer in a network, the port number is used to identify each service on a computer.
See Also
A port is a virtual point where network connections start and end. Ports are software-based and managed by a computer’s operating system. This is in contrast to the MAC address which is hardware based. Each port is associated with a specific process or service running on it.
Using a port number allows computers to easily differentiate between different kinds of traffic being generated.
Ports are unique on each individual computing device. But a different computer can use the same port number. The way they differentiate is by the combination of IP Address and the port number.
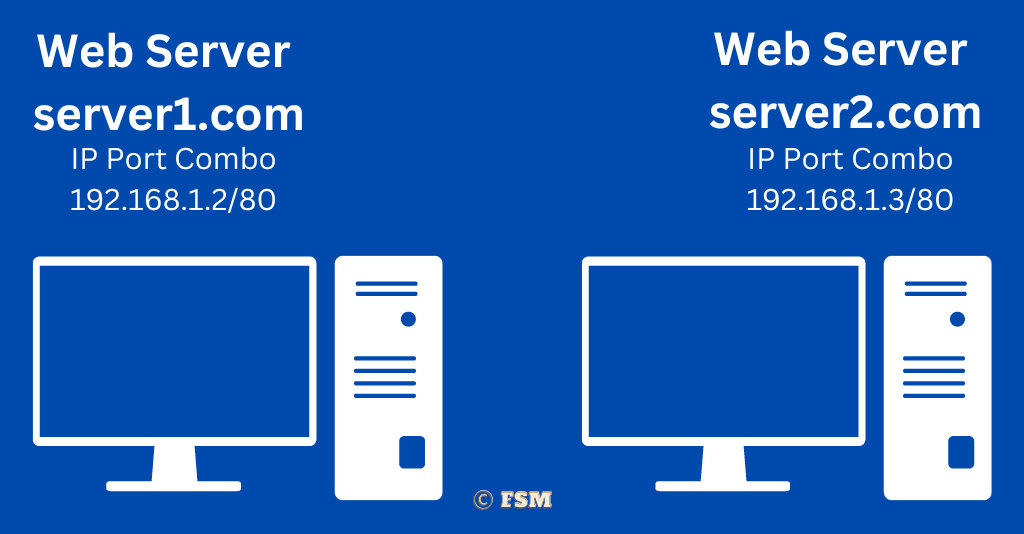
To understand this better consider the setup shown in the image above. It shows a web server for domain server1.com running on a server. Next to it, the other server is running a web server for the domain server2.com. Both of these servers are using port 80 to service incoming requests.
They way this works is that since an IP address is unique to a computer we are able to use that with the same port 80 on both servers to serve different domains.
More on Port Numbers
Each port has a unique number ranging from 0 to 65535. These port numbers are used to identify the specific applications and services that consume, produce or both consume and produce data.
When two devices communicate over a network, they do so by establishing a connection through their respective ports. This is called binding to a port. This port binding mechanism blocks multiple applications from connecting and using the same port number.
What are the Different Types of Port Numbers
Ports are categorized into four distinct types based on the actual port number and its usage.
Well Known TCP/IP Ports
These are numbers between 0 and 1023. Well known ports are reserved for widely used protocols and services. Examples of well know or commonly used ports are 80 (for HTTP), 25 (for SMTP) and 22 (for SSH).
Registered Ports
Registered ports are in the range 1024-49151 and are used for non-system services. These ports are assigned by IANA for specific applications and services. Examples of services that use registered ports include IMAP (port 143), POP3 (port 110) and FTP (port 21).
Dynamic or Temporary Port Numbers
Dynamic ports are in the range 49152-65535 and are used for temporary or ephemeral services. These ports are generally used during establishing a connection with a new client.
For example an application using the Torrent protocol uses dynamic ports during communication for anonymity and security purposes. Once the active session completes, the dynamic port is released back to the operations system and is available for use by other applications.
Private Ports
Private ports are not assigned by any central authority. These are used by companies for internally hosted services. Normally port numbers above 1024 and above are used if needed for internal applications.
What is The Difference Between IP Address and Port Number?
An IP address identifies a machine in a TCP/IP network and is unique within a subnet. Port numbers are used to identify a particular application or service on a system.
| IP Address | Port Number |
|---|---|
| IP Address is used to identify a computer (host) on a specific number. | Port number is used to identify a process binding on a specific computer. |
| IP Address is unique across a subnet. | Port is unique only on a single computer. |
| IP v4 address use 32-bits (4 bytes). IP v6 addresse use 128-bits (16 bytes) | Port numbers use 16-bit (2 bytes) |
| Example of an IP address: 192.168.1.1 | Example of a port number: 80 |
| Maximum unique IP addresses: When using a class C IP range, the maximum numbers of IP addresses is 2,097,152. | Maximum number of unique port numbers on a computer: 65536 |
Commonly Used Port Numbers
Shown below is a list of some of the most commonly used port numbers.
- DNS (Domain Name System): Port 53 is the default port for DNS, used for resolving domain names to IP addresses.
- FTP (File Transfer Protocol): Port 21 is the default port for FTP protocol, used for transferring files.
- HTTP (Hypertext Transfer Protocol): Port 80 is the port for HTTP traffic.
- HTTPS (Secure Hypertext Transfer Protocol): Port 443 is the HTTPS (SSL) traffic.
- POP3 (Post Office Protocol version 3): Port 110 is used for POP3 email.
- SMTP (Simple Mail Transfer Protocol): Port 25 is for SMTP email.
- SSH (Secure Shell): Port 22 is used for secure remote login to servers.
These are just a few examples of common port numbers in networking. Check our well know ports page for a list of the most commonly used ports.
TCP vs UDP Ports
TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are two different base protocols built for network communication in TCP/IP networks. The main difference between them is that one is connection-oriented and the other is not. two is the way they handle data transmission and ensure reliable data delivery.
| TCP | UDP | |
|---|---|---|
| Data Transmission | TCP is a connection-oriented protocol that establishes a reliable connection between two devices before transmitting data. For transmission data is transmitted in segments (or packets). Any lost data segment is re-tranmissted to avoid data corruption. | UDP is a connectionless protocol that does not maintain a live connection during reliable connection before transmitting data and does not guarantee the delivery of data packets. |
| Reliability | TCP is considered a reliable protocol as it guarantees the delivery of data by retransmitting lost or corrupted packets. TCP uses a mechanism of a sliding window transfer protocol. | UDP, is considered an unreliable protocol as it does not guarantee the delivery of data packets. The responsibility of the maintaining data integrity is that of the client application. If a packet is not received the client can request the server to resend the lost data packet. |
| Speed | TCP is slower than UDP because of the overhead required to establish and maintain a reliable connection and to retransmit lost or corrupted packets. | UDP is faster because it does not need an ACK acknowledgement for data packets sent to a client. |
| Use Case | TCP is used for applications that require reliable data delivery, such as email, file transfers, and web browsing. | UDP is commonly used for applications that require fast and efficient transmission of data, such as streaming media and online gaming. |
What is Port Blocking?
Port blocking is a process where a software or hardware firewall is used to block, filter or secure network traffic based on user-defined rules.
Firewalls usually sit between a trusted network and an untrusted network. Although it can be used in cases where a firewall is placed between multiple secured and trusted networks and is used as an access control layer.
Firewalls are also used to block internal applications using ports that are vulnerable to attack by hackers. For example, the port being used by the LDAP directory server used for managing internal logins has no reason for being exposed to the public internet where the company data can be accessible to a hacker who is able to exploit a vulnerability in the LDAP protocol.
A good practice for managing port access is to have all ports blocked by the firewall and only opened if there is a business need.
Port Forwarding in TCP/IP
Port forwarding is another technique used to redirect incoming data packets from one server to another on the same or a different network.
Port forward can be considered a cloaking mechanism where you may hide the identity of a server by using another in the middle of the communication to provide security and scalability.
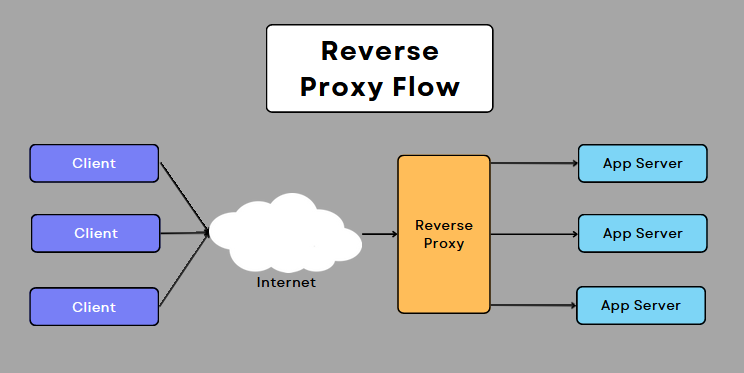
In the above image, the reverse proxy is set up to forward incoming HTTP/HTTPS requests to multiple backends providing load balancing service. Check out my post on NGINX proxy to learn more about configuring a Proxy Server for stability and security.
The benefits of port forwarding include:
- Improved security by filtering out malicious attempts to access internal resource.
- Remote access to internal services to outside clients.
- Better network performance through load balancing.
- Increased functionality through remote management and monitoring.
In conclusion, port forwarding is a useful technique in TCP/IP networking that allows network administrators to redirect incoming data packets to a specific internal device or service. The benefits of port forwarding include improved security, remote access, better network performance, and increased functionality.
Conclusion
To summarize, ports are software abstraction that provides the ability to communicate over the physical network.
Frequently Asked Questions
What is the difference between an open and closed port?
Ports can be classified as either open or closed. Open ports are those where an application service is actively listening for new connection requests. Closed ports are those which are not currently being used.
You can use the netstat command in Windows to view active TCP and UDP connections.
netstat command is also available on Linux based systems such as Ubuntu and RedHat.
What is the port number for localhost?
Localhost is the default name used to establish a connection with a computer. The IP address is usually 127.0.0.1.
A complete range of ports (0-65535) is available to applications on the computer to be used in conjunction with localhost.
What is port number 8080 used for?
Port number 8080 is usually used by web servers during development and testing. Port 8080 is also in production servers when sitting behind a firewall setup with port forwarding.
Many Java application servers such as Apache Tomcat use port 8080 in their default configurations.
What is a Proxy Port?
A proxy server is, essentially, a computer on the internet with its own IP address. It sits between a network client and a remote server while acting as an intermediary to handle requests.
When a user request comes into a firewall or proxy, it is accepted for processing. The incoming request is forwarded to a backed server which processes the request, the results of which are then forwarded to the requesting client.
Proxy port thus is the port setup on the server handling incoming client requests. This hides access to the IP and port of the backend server.
What is my IP address and port number?
Your IP address is one that is assigned to your computer by your Internet Service Provider (ISP). The port number you are using depends on the service you are accessing. If you are going to a browser to view content on Google, then the remote port you are using is 80.
You can view your public IP address using our IP lookup tool.
What is the port number for Gmail SMTP?
Gmail uses both Internet Message Access Protocol (IMAP) and SMTP.
- Incoming IMAP Port: 993
- Outgoing IMAP Port: 465 for SSL and 587 for TLS/STARTTLS: 587
- SMTP Port: 25, 465, or 587