Nmap is a powerful command line tool network scanning tool that is used to identify open ports, services, and vulnerabilities on a network.
Nmap works by sending packets to target hosts and networks and analyzing the responses or the lack thereof.
The primary use for nmap is to do port scanning, which involves scanning a range of TCP and UDP ports to determine open, closed, and filtered ports. By identifying the status of each port, network administrators can get information about network layout, available services, and existing vulnerabilities.
See Also
In this article, we will explore the basics of using Nmap for port scanning and some of its more advanced features and techniques.
Let’s start!
How to Install Nmap
The first step before using Namp is installing the tool locally. Depending on the operating system you are using, the process will be different. Nmap supports FreeBSD, Linux, MacOS and Windows platforms. Let’s go over the details of installing the program on a couple of them.
Install Nmap on Linux
On Linux, Nmap comes as a built in package and can be installed using the apt package manager. Use the command below to install Namp on Ubuntu:
user@mars:~$ sudo apt install nmapThis will install the Nmap and all dependencies. You can read the man page using the command man nmap.
You should also install ndiff, a utility used to compare XML output from different Nmap runs to highlight differences.
user@mars:~$ sudo apt install ndiffInstall Nmap on Windows
To install Nmap on Windows you need to go to the Nmap website.
Listed below are the steps.
- Download Nmap installer.
- Locate the installer in your Downloads folder.
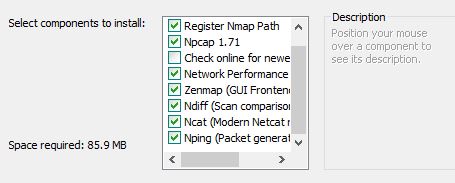
- Run the installer and follow the instructions to install it on your local machine.
Note: On Windows additional utilities are installed, including Zenmap, the official UI for Nmap.
All executable files are in the root install folder.
Install Nmap on MacOS
There are multiple ways to install Nmap on MacOS. One way is to download the install files from the Nmap website and follow the standard install procedure. The download is available as a .dmg file and you can double-click it to install it on your local machine.
- Download the installer.
- Double-click on the .dmg file to start the installation.
- Follow the instructions to complete the setup.
Basic Nmap Port Scanning with Examples
With the Nmap utilities installed on my computer, I am ready to start actual scanning using the Nmap tools.
Before starting check the Nmap documentation to understand all the options. You can view online documentation here. It is available in multiple languages.
Nmap Command Syntax
Nmap use the following command line options syntax:
nmap [scan type] [options] [target]The scan type specifies the type of scan to perform. The following scan types are available:
| Scan Type | Scan Option |
|---|---|
| TCP SYN/Connect()/ACK/Window/Maimon scans | -sS/sT/sA/sW/sM |
| UDP Scan | -sU |
| TCP Null, FIN, and Xmas scans | -sN/sF/sX |
| Idle Scan | -sI |
| SCTP INIT/COOKIE-ECHO scans | -sY/sZ |
| IP protocol scan | -sO |
| FTP Bounce Scan | -b |
You can customize these scan flags by using the --scanflags option.
To run any type of scan on a single host, provide the IP address after the scan type.
TCP Connect Scan
An example of a TCP Connect scan with output is shown below.
user@mars:~$ nmap -sT 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:04 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000042s latency)./ubuntu focal/main amd64 python3-bs4 all 4.8.2-1 [83.0 kB]
All 1000 scanned ports on localhost (127.0.0.1) are closedthon3-webencodings all 0.5.1-1ubuntu1 [11.0 kB]
Get:4 http://archive.ubuntu.com/ubuntu focal/main amd64 python3-html5lib all 1.0.1-2 [84.3 kB]
Nmap done: 1 IP address (1 host up) scanned in 0.04 secondsmd64 python3-lxml amd64 4.5.0-1ubuntu0.5 [1384 kB]TCP SYN Scan
TCP SYN scan is the most common scanning technique. It works by sending the SYN packet to target a host and then analyzes the response.
It is a fast and stealthy technique used to identify open ports.
In the example below, I am using Nmap to do a SYNC scan for all ports on a specific IP address. You can replace the IP address with a hostname as well.
user@mars:~$ sudo nmap -sS 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:17 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.0000030s latency).
All 1000 scanned ports on localhost (127.0.0.1) are closed
Nmap done: 1 IP address (1 host up) scanned in 0.18 secondsHere you can see that Namp scans 1,000 ports in about 0.18 seconds.
Scan a Single Port on a Host or IP Address with Nmap
Use Nmap with the -p option to test a single port or a specific range of ports.
user@mars:~$ nmap -p 80 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:22 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.00018s latency).
PORT STATE SERVICE
80/tcp closed http
Nmap done: 1 IP address (1 host up) scanned in 0.03 secondsScan Multiple Ports on a Host with Nmap
I will use the -p option with a range to port scan multiple ports on a host.
user@mars:~$ nmap -p 80-85,443 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:25 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000042s latency).
PORT STATE SERVICE
80/tcp closed http
81/tcp closed hosts2-ns
82/tcp closed xfer
83/tcp closed mit-ml-dev
84/tcp closed ctf
85/tcp closed mit-ml-dev
443/tcp closed https
Nmap done: 1 IP address (1 host up) scanned in 0.03 secondsIn the example above, I am scanning for port range 80-85 and port 443 on localhost (127.0.0.1)
UDP Port Scanning with Nmap
UDP scan works in a similar way to TCP SYN scan but is used to identify accessible UDP ports. Keep in mind that UDP scan can be slower and less reliable than TCP scans.
To run a UDP port scan use the following command option:
user@mars:~$ sudo nmap -sU 127.0.0.1Open Port Scan with Namp using IP Addresses From a File
To scan open ports for multiple IP addresses you can use a file with IP addresses as input to Nmap.
user@mars:~$ sudo nmap -sS -iL ipads.txt
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:33 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.0000030s latency).
All 1000 scanned ports on localhost (127.0.0.1) are closed
Nmap done: 2 IP addresses (1 host up) scanned in 3.38 secondsIn the IP addresses file, enter each IP Address on a separate line.
Now that you are acquainted with some of the basic port scanning techniques with Nmap, let’s look at some advanced Nmap port scanning options.
Advanced Nmap Port Scanning
Nmap also supports a variety of advanced scanning techniques that can provide more detailed information about the target host and its vulnerabilities.
Service Version Detection with Nmap
The first one we will look at is version detection.
Version detection is a technique used by Nmap to identify the specific software versions and services running on open ports. This can be useful for identifying potential vulnerabilities and determining the best approach for exploiting them.
This will perform a TCP SYN scan with the -V option to identify the versions of the services running on open ports.
I will now run this command on a Windows workstation.
C:\apps\misc\nmap>nmap.exe -sV 127.0.0.1
Starting Nmap 7.93 ( https://nmap.org ) at 2023-03-07 13:41 Pacific Standard Time
NSOCK ERROR [0.0660s] ssl_init_helper(): OpenSSL legacy provider failed to load.
Nmap scan report for aitech.news (127.0.0.1)
Host is up (0.00026s latency).
Not shown: 988 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http nginx 1.23.3
90/tcp open http Apache httpd 2.4.50 ((Win64) OpenSSL/1.1.1l PHP/8.1.11)
135/tcp open msrpc Microsoft Windows RPC
445/tcp open microsoft-ds?
543/tcp open http Apache httpd 2.4.50 ((Win64) OpenSSL/1.1.1l PHP/8.1.11)
902/tcp open ssl/vmware-auth VMware Authentication Daemon 1.10 (Uses VNC, SOAP)
912/tcp open vmware-auth VMware Authentication Daemon 1.0 (Uses VNC, SOAP)
3306/tcp open mysql MySQL 5.5.5-10.6.7-MariaDB
5432/tcp open postgresql PostgreSQL DB 14.1 - 14.5
9010/tcp open websocket WebSocket++ 0.8.2
9080/tcp open glrpc?
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 12.55 secondsOS Fingerprinting with Nmap
OS Fingerprinting OS fingerprinting is a technique to identify the operating system running on the target host. To perform OS fingerprinting using Nmap, use the -O option with Nmap.
This will perform a TCP SYN scan and identify the operating system running on the target host.
user@d1:~$ sudo nmap -O 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:49 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000051s latency).
Not shown: 996 closed ports
PORT STATE SERVICE
80/tcp open http
443/tcp open https
631/tcp open ipp
3306/tcp open mysql
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6.32
OS details: Linux 2.6.32
Network Distance: 0 hopsThe above example running on Ubuntu show the open ports with the information about the Operating system.
Although, I found this is not a fool proof method. Running the command on Ubuntu (WSL host), return a message stating that too many fingerprints to give specific OS details.
sohail@mars:~$ sudo nmap -O 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:45 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000037s latency).
All 1000 scanned ports on localhost (127.0.0.1) are closed
Too many fingerprints match this host to give specific OS details
Network Distance: 0 hops
OS detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 1.82 secondsUsing Timing Options with Nmap to Control Speed of Scan
Us the -T option with Nmap to adjust timing options. The number ranges between 0-5, with a higher number suggesting a faster and more agressive speed of scan.
In the example below, I will use TCP SYN scan with a timing option of 5.
user@mars:~$ sudo nmap -sS -T5 127.0.0.1
Starting Nmap 7.80 ( https://nmap.org ) at 2023-03-07 13:58 PST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.0000030s latency).
All 1000 scanned ports on localhost (127.0.0.1) are closedFaster scans are easier to detect with Intrusion Detection Systems (IDS)
Using Nmap Script to Perform Advanced Scanning
Nmap scripts are pre-written scripts that can be used to perform more advanced scanning techniques.
These scripts can be downloaded from the Nmap Scripting Engine (NSE) repository and used with the -sC option.
For example you can run the brute-force password cracking using the command below.
sohail@mars:~$ sudo nmap -sS -C ssh-brute 127.0.0.1Listed below are some of the scripts available for Nmap. You can view the complete list here.
- auth
- broadcast
- brute
- discovery
- dos
- intrusive
- malware
Nmap GUI and Other Tools
Nmap is a powerful command line tool used for open port scanning. Due to its nature, it can be part of scripts when automation with scanning is desired.
But there are cases where a GUI provides a more user-friendly interface, especially for beginners.
Luckily, there are multiple GUIs available that sit on top of Nmap. Below is a list of available options.
- Zenmap: It is now bundled with Nmap and provides a very easy to user interface. It provides additional features such as saving scan results and comparing multiple test run results visually. It runs on Windows and Linux.
- Nmapsi4: Nmapsi4 is another GUI for Nmap that provides a more comprehensive interface for performing scans. You can use it to perform scans. It is built on top of the Qt library and runs on systems that support this feature.
- Nmap Online: This is a paid service, accessible through a web-based interface. It has more usability features when compared to some of the other tools in this list.
- Metasploit Framework: This is a popular open-source penetration testing tool that includes several modules for port scanning and network exploration using Nmap. This is the most featureful tool in this list.
Write About Port Scanning Techniques
Multiple techniques are available to do open port scanning. Each has its own purpose and pros and cons. Although I have listed the names earlier, let me get into a bit more detail about scanning techniques in this section.
- TCP Connect scan involves attempting to establish a full TCP connection with the target host on each port. This is slower but a more accurate scanning strategy. It can identify which services are available on the open ports. It is also less likely to be detected by an IDS system.
- TCP SYN scan, aka a half-open scan, involves sending a SYN packet to the target port. If an SYN-ACK pack is received in reply then it shows that the port is open and waiting for a connection. If the port is not open then an RST response packet is sent back. It is faster than a TCP connect scan but does not provide detailed information such as service listening on a port.
- UDP scan sends traffic over a UDP connection to a port. If the port is closed then an ICMP message is sent back showing that the port is closed and not accepting incoming connection requests. A UDP scan is slower and less reliable than a TCP scan.
- Null scan sends a network packet with no flags set to the target port. host on each port in the scan range. If the port is open, the target will not respond. If the port is closed, the target will respond with an RST packet. A Null scan is faster than a TCP SYN scan, but it is also more likely to be detected by IDS systems. This is because Null scan traffic is considered unusual and thus tagged as suspicious.
- XMAS scan sends a packet with the FIN, URG, and PUSH flags set to the target port. Only if the port is closed the target will respond with an RST packet. XMAS scan is also faster than a TCP SYN scan and is also more likely to be detected due to the unusual nature of the traffic it generates.
On my post on hacking, you can get more details of port scanning techniques with examples.
Summary
Nmap provides a powerful command-line interface to user for scanning open ports. Using available interfaces that use namp on the backend additional features can be added to Nmap.
It is one of the most commonly used port scanning programs available for free with an open source license.