In an increasingly connected world, preventing malicious activity in networked environments is critical to maintaining the security and confidentiality of sensitive information. Port scanning is a common method attackers use to identify open,closed and filtered ports on a target system, and it’s a precursor to more malicious activity, such as exploiting vulnerabilities or launching denial-of-service (DoS) attacks.
Thus, detecting port scanning is increasingly being used in active and passive implementations to secure network environments.
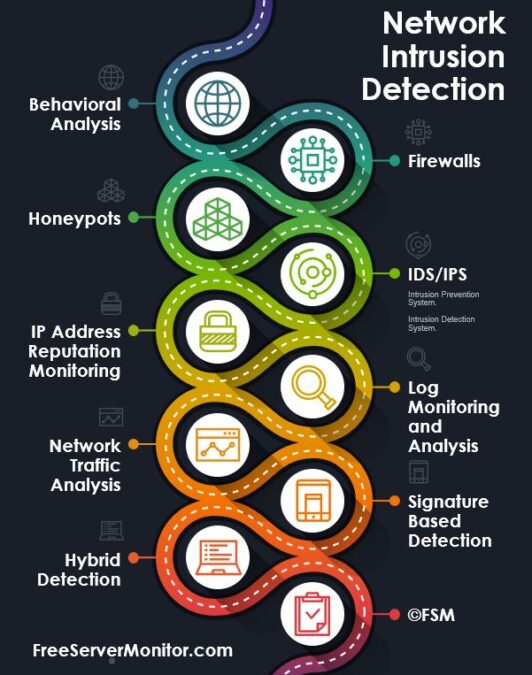
In this post, I will go over the details of various types of port detection methods.
- Types of Port Scan Detecting Methods
- Different Methods of Detecting Port Scan Activity
- Best Practices For Detecting Port Scans
- Conclusion
Types of Port Scan Detecting Methods
There are two main types of port scanning detection methods and using those a derived third type also exist.
- Active: Active detection methods are another approach to detecting port scans. Unlike passive methods, active methods interact directly with the source of the traffic to determine if a port scan is being attempted
- Passive: These methods are designed to monitor network traffic without directly engaging with the source of the traffic. They analyze network packets to determine if a port scan is being attempted. Unlike active detection methods, passive detection methods do not generate any additional network traffic and do not produce any responses to the potential attacker
- Hybrid:
- Hybrid detection methods combine the strengths of both passive and active detection methods to improve the accuracy and efficiency of detecting port scans. They are designed to detect port scans by monitoring network traffic passively while also generating some network traffic to actively probe the source of the traffic. Hybrid detection methods typically involve a two-stage process involving passive monitoring and active probing.
Check out my post for details on what port scanning is and additional info with examples of the different types of port scans.
Different Methods of Detecting Port Scan Activity
There are various methods of detecting port scanning activities, with each offering its own pros and cons. The selection of the best methods for detecting a port scan will depend on the specific security needs and on the type of network.
Behavioral Analysis
Behavioral analysis is an effective method for detecting port scans and other types of network-based attacks. In behavioral analysis patterns in network traffic are identified and anomalies are flagged to indicate a potential security threat. This work in active mode in real-time.
Tools using behavioral analysis are trained for known network patterns. For example, when a port suddenly starts to receive a large number of incoming network requests from one or more IP addresses in a short period of time, this unusual pattern of network traffic is flagged, and logged with notifications sent to monitoring staff. This type of anomaly in traffic can easily be detected using network behavioral analysis.
Behavioral analysis can be performed using Intrusion Detection Systems (IDS), which are designed specifically for network traffic analysis. IDS tools can be configured to monitor network traffic in real-time and detect patterns of behavior that indicate a potential security threat.
Once a security threat has been detected, the IDS can take action to prevent further attempts of network intrusion. IDS tool can:
- Alert network administrators and monitoring staff.
- Automatically block all incoming network traffic from the malicious IP address(s).
- Or limit the type of traffic allowed.
Behavioral analysis can also be used in hybrid detection approaches with other security solutions.
Pros and Cons of Behavioral Analysis
| Pros | Cons |
|---|---|
| Detects previously unknown attacks: Behavioral analysis is effective at detecting port scanning attempts that are not easily identified by other methods. | Resource intensive: Requires large amount of processing and memory resources to analyze all the data passing through a network. |
| Dynamic approach: Behavioral analysis systems work by rules and patterns. This flexibility allows such tools to be effective at detecting evolving and new threats. | High expertise: Requires deep understanding of network protocols, data structures, and attack patterns. This requires trained staff to manage and configure behavioral analysis systems. |
| Low occurrences of false positives: By focusing on behavior instead of specific signatures, the number of false positive alerts is reduced. | Difficult to fine-tune: Even with expert knowledge the rules require fine-tuning based on the type of network and organization needs. A rule working for a use case for one service may not be effective at identifying threats for a different type of web service. |
Firewalls
At its core, a firewall is a network security apparatus used for allowing or blocking network traffic on a port. As the role of firewalls evolved further functionality such as port filtering was added.
Firewalls are a simple yet elegant solution for reducing the risk of port scanning and network intrusion, by analyzing incoming and outgoing network traffic and blocking any traffic that does not meet a specific set of rules or policies.
Firewalls can be used to block or limit all incoming traffic from IP addresses that are known to be associated with malicious activities, such as port scans. For example, a network may only want to allow access to a hosted HTTP or HTTPS web service on a specific port number to only people within the internal network, while blocking all traffic from external public networks.
Firewalls can also be used to monitor network traffic for suspicious activity, such as a large number of incoming connections from a single IP address, which can indicate a port scan. Automated actions such as blocking the suspicious IP address can be taken by the firewall. This is similar to the behavioral analysis approach albeit in a limited fashion.
Firewalls are not a replacement for other security measures, such as log monitoring and analysis and other IDS systems. Instead, firewalls should be used in conjunction with other security measures to provide a more comprehensive hybrid security solution.
Pros and Cons of Firewall Detection Systems
| Pros | Cons |
|---|---|
| Effective in blocking known threats. | Limited protection against unknown threats. |
| Port blocking and filtering rules are easy to set up. | Due to the ease of implementation of a firewall, it can lead to a false sense of security where organizations may neglect other more effective security measures. |
| Centralized management. | Can slow network performance. |
Vendors Providing Firewall Solutions
Below is a list of companies providing firewall solutions for all types of enterprises.
- Barracuda Networks
- Cisco
- F5 Networks
- Forcepoint
- Fortinet
- Palo Alto Networks
- SonicWall
- Versa Networks
- WatchGuard
Honeypots
A honeypot is a decoy system designed to attract attackers away from the main network to collect information about their activities. Usually, the goal is to gain insights into the entity attacking the network system and distract them away from accessing the main system.
Honeypots set in this manner help to prevent or reduce port scanning and other types of attacks from occurring on the main network. Honeypots provide valuable information about the types of attacks being conducted and the methods used. This information can further be used to improve the security of the network and identify the location (network and geo) of the attacker to prevent future attacks.
Pros and Cons of Honeypot Detection Systems
| Pros | Cons |
|---|---|
| Early detection of attacks: Used to detect and respond to attacks before they have a chance to spread to other systems. | Complex to set up and maintain: Honeypots are usually complex and expensive to set up and maintain. Require extra hardware, software and personnel resources. |
| Low impact on production systems: Since malicious traffic from the main network system is diverted to the honeypot, the impact on production systems is reduced. | Potential to attract unwanted attention: Since the purpose of a honeypot is to attract potential attackers to the honeypot, organizations increase the risk of unwanted security intrusions. |
| Improved understanding of attacker behavior: Helps organizations improve their security measures and reduce the risk of future attacks. | False positive alerts: Honeypots can generate false positive alerts. |
Intrusion Preventions Systems (IPS) / Intrusion Detection Systems (IDS)
An IDS is a software solution designed to detect security threats, including port scans and other types of network attacks, and alert on potential security threats.
Whereas an IDS is considered by some as a passive solution, an IPS system, also referred to as an Intrusion detection prevention system (IDPS) works by continuously monitoring network traffic for suspicious activity and taking steps to prevent it.
An IDS can be configured to detect the following activities related to a port scan:
- Excessive Incoming Connections: Unexpected rise in incoming traffic to a port from an IP address may indicate a port scan. Sometimes this type of attack can come from multiple IP addresses. Either way and IDS can be configured to detect this excessive rise in traffic and provide an alert.
- Increased Error Messages: An increased number of error messages occurring on the network can indicate an active port scan attack.
- Unexpected Port Activity: Traffic on closed ports or on filtered ports can indicate a port scan.
By detecting these indicators, an IDS can provide important timely alerts, so steps can be taken to prevent continuing attacks.
In addition to detecting port scans, an IDS can also be configured to detect other types of network-based attacks, such as malware infections, denial of service (DoS) attacks, and unauthorized access attempts.
It is important to note that an IDS is not a replacement for other security measures, such as firewalls and log analysis tools. An IDS solution should be used in conjunction with other security measures to provide a comprehensive security solution.
Pros and Cons of Intrusion Detection Systems
| Pros | Cons |
|---|---|
| Real-time detection: IDS provides real-time detection of port scanning and other malicious activity. | High false positive rate: Generates a high number of false positive alerts, making it difficult to distinguish between real threats and harmless activity. |
| Improved visibility: Provides a comprehensive view of network activity, helping identify potential security threats. | Resource-intensive: Requires significant processing power and storage capacity to operate effectively. |
| Easy to deploy: Relatively easy to deploy, requiring minimal configuration and setup. | Dependence on signatures: Predefined signatures limit the effectiveness against new, evolving and unknown threats. |
Vendors Providing IPS and IDS Solutions
Below is a list of companies providing firewall solutions for all types of enterprises.
- SolarWinds Security Event Manager
- OSSEC: Open source platform
- Suricata: Open source platform.
- Security Onion
- Trellix
- Palo Alto Networks
- Zeek (formerly Bro): Open source platform.
IP Address Reputation Monitoring
IP address reputation is a method of detecting security threats, including port scans, by evaluating the reputation of the source IP or Network address.
Using IP Address monitoring address means maintaining a list of malicious IP addresses and checking incoming network traffic against this database. If an incoming network packet originates from an IP address that is known to be associated with malicious activity, the network traffic can be flagged for further analysis or blocked completely.
There are multiple blacklists maintained by various organizations and one can subscribe to those for changes.
Check our IP Address Blacklist tool to see if an IP or domain is listed Blacklisted.
Read more about Blacklists and how to remove an IP address from a Blacklist.
Using IP address reputation lists malicious attackers can quickly be identified and prevented from entering the network.
Pros and Cons of IP Address Reputation Monitoring Systems
| Pros | Cons |
|---|---|
| Easy to implement: IP address reputation lists are easy to use and implement. | Limited scope: IP address reputation covers only a limited scope of network activity. With the advent of cloud computing, it is very easy to get a new IP for network scanning. |
| Accurate: Once an IP address is identified as malicious it is only a matter of adding it to the blacklist. All traffic from that IP can be blocked. | False negatives: Blacklists are error prone. Some IPs can be put on these lists and never removed even when the threats are gone. With DHCP a non-fault IP address can be blocked. |
| Cost-effective: IP address reputation is a cost-effective solution as most Blacklists are freely available. | Relying on third-party data: IP address reputation systems rely on data from third-party sources, which can sometimes be inaccurate or outdated. |
Log Monitoring and Log Analysis
Log monitoring tools analyze network logs, identifying patterns of suspicious activity and access to identify port scanning activity. Using this information necessary steps can be taken to prevent future attacks.
Following are some ways of using log monitoring systems to strengthen network protection:
- Excessive Incoming Connections: A large number of incoming requests in a short time, from a single IP address, can indicate port scanning activity.
- Increasing Error Messages: An increase in error messages can indicate a port scan. Although this could also be a valid network.
- Unexpected Port Activity: Unexpected traffic on a closed or filtered port can indicate a port scan. For example, if a normally closed port starts receiving incoming traffic, this could indicate a port scan.
- Suspicious IP Addresses: Network logs can be used to identify suspicious IP addresses, associated with port scans.
Pros and Cons of Log Analysis and Monitoring Systems
| Pros | Cons |
|---|---|
| Detailed information: Log analysis and monitoring provides extensive information about network activity, including source, destination, and type of traffic. | Data Overload: Log analysis and monitoring require tools to do log analysis because of large amounts of data. |
| Real-time monitoring: Limited semi-real-time analysis can be done with log captures. | Limited Accuracy: Logs may not always be complete or accurate. Only relying on a single factor such as an increase in error messages could be indicative of a possible issue with valid network issues. |
| Cost-effective: Basic Log analysis does not require expensive equipment or software. | Time-Consuming: Extensive log analysis is time consuming and requires specialized skills. |
Network Traffic Analysis
Using network traffic analysis one can identify the presence of an active scan by observing the types, sequences and frequency of network packets being sent to multiple ports in a short period of time. One can also analyze targeted activity on a single port as well.
Based on the decision taken by the software, traffic from the source IP address can be blocked for a certain time period. Repeated incursion from the same IP may result in a permanent block with the IP added to a Blacklist.
Network traffic analysis is used with other security threats such as distributed denial of service (DDoS), data exfiltration and malware attacks.
There is an overlap in how network analysis and behavioral analysis work.
Network traffic analysis does have its limitations. Large amounts of traffic on the network means a significant cost of hardware and software to maintain such infrastructure. Although longer term cost of personnel likely will end up being higher than the cost of the other hardware or software itself.
Pros and Cons of Network Traffic Analysis
| Pros | Cons |
|---|---|
| Comprehensive: Provides comprehensive coverage of all network traffic, helping to detect even the most advanced port scanning attacks. Detecting both known and unknown port scanning techniques makes this an effective method of detection. | Resource Intensive: Analyzing all network packets is not a cheap computational task. A lot of computing resources need to be dedicated to analyzing network traffic. Since all traffic passes through the analysis system, results in a slightly slower network, which depending on business needs may not be the best option. |
| Realtime: Detects port scanning attempts in real-time, which allows quick response to prevent existing and future attacks. | Complexity: Systems can be complex to configure, requiring expertise in the domain. This makes it difficult for smaller organizations to implement network analysis systems. |
| Forensic Analysis: Due to the large amount of data captured with traffic analysis, advanced detection strategies can be built to enhance functionality. Data from network traffic analysis can be used to train advanced AI models to detect complex attack strategies. | False Positives: This can generate false positives, which lead to alerts that may not be valid and are time-consuming to investigate manually. |

Pattern or Signature-Based Detection
Signature-based detection is a method of identifying security threats including port scans. It does so by comparing incoming network traffic against a database of known security threats. These pre-compiled patterns or signatures associated with prior malicious activity trend help identify port scanning attempts.
The signature-based approach is effective at detecting known and widely used port scanning tools used to identify scanning attempts, as the signatures for these are already known.
However, there are certain limitations. For example, new port scanning techniques and tools are constantly being developed. Capturing and identifying the new signatures of these new techniques take time and thus introduces a delay in adding them to the signature database. But even with such limitations over 80% of attacks can be blocked as they use existing patterns and signatures.
Pros and Cons of Signature-Based Detection Strategies
| Pros | Cons |
|---|---|
| Effectiveness: Signature-based methods are highly effective in detecting known port scanning attempts. These look for existing patterns making it easy to detect network intrusion. | Limited Scope: Signature-based systems can only detect known port scanning tools and techniques. These are best used with additional port scanning detection techniques. |
| Quick to respond: When a specific signature is detected, the system can immediately trigger an alert. | False Positives: Legitimate network traffic can appear similar to port scanning activity, such as a large number of outgoing packets with different source ports. |
| Customization: Signature or pattern based techniques can be used to detect specific port scanning tools. This can make the system more effective in detecting attacks. | Maintenance: Regular maintenance to required to ensure that the system is up to date with the latest patterns and signatures. Although some modern solutions are using auto updates to signature databases to reduce administration costs. |
Hybrid Detection
Hybrid detection strategies combine various detection models to build more comprehensive and effective solutions against port scanning attacks. By utilizing the strength of multiple scanning techniques better systems can be designed to reduce false positives and provide higher accuracy in detecting port scans.
A few examples of common combinations for hybrid strategies are:
- Signature-based detection with network traffic analysis.
- Intrusion detection systems (IDS) with log monitoring and analysis
- IP address reputation with behavioral analysis
Pros and Cons of Hybrid Port Detection Approaches
| Pros | Cons |
|---|---|
| Increased accuracy. | Higher resource usage. |
| Reduced false positives. | Implementation complexity. |
| Comprehensive coverage. | False negatives. |
Best Practices For Detecting Port Scans
Detecting port scans is a critical component of protecting network security. Here are some best practices for detecting port scans:
- Monitor Network Traffic: Monitor network traffic to identify abornormal traffic patterns.
- Set Up Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): Set up IDS and IPS to detect and unwanted network intrusion. Alerts should be set to trigger on detected attempts of port scanning.
- Monitor System Logs: Implement log monitoring as a method to do a forensic analysis of user activity and application servers access and usage.
- Implement Firewall Rules: Use firewalls as first layer of defense against unwanted attacks.
- Use Port Scanning Tools: Use port scanning tools actively to identify vulnerabilities within your own network.
- Regularly Update Security Software: Regularly update all security system software. Ensure that all rules and signature databases are also up to date with the most recently identified threats.
- Perform Regular Network Assessments: Regular network assessments can help identify any changes in network traffic patterns or unusual activity that may indicate a port scan.
Conclusion
It is important to regularly monitor and update the security measures in place to protect against port scans. Although deploying port scan detecting software and tools is a great way to protect your network, I personally feel that it comes secondary to taking a proactive approach where you actively try to break your own network by deploying the same techniques a hacker would use.
Using your own testing will provide information on the exact weaknesses in your network. By securing these weak links you are able to address risks before they become real issues in production environments.
Once internal testing is complete, I would suggest taking a hybrid approach to network security to benefit from the strength of different methods.
Let me know in the comments what approach your company is taking to protect your network from intrusion.